Wireshark,Wireshark is a loose software you use to capture and think about the data visiting backward and forward in your network.
This open-source protocol analyzer is widely everyday as the industry widespread, winning its truthful percentage of awards through the years.
Originally called Ethereal, Wireshark has a consumer-friendly interface that,
may show records from hundreds of various protocols on all essential network types.
Wireshark supports dozens of seize/hint file codecs supported together with CAP and ERF. Integrated decryption tools permit you to view encrypted packets for several popular protocols along with WEP and WPA/WPA2.
Wireshark,Downloading and Installing Wireshark
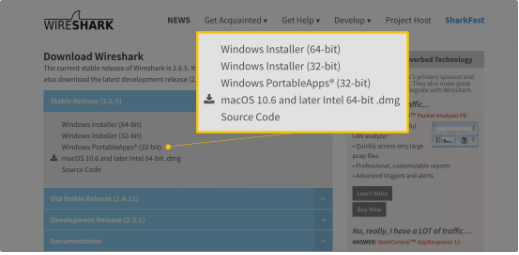
Wireshark,Wireshark may be downloaded without charge from the Wireshark Foundation internet site for both macOS and Windows working systems.
During the Windows setup process, you need to pick to put in WinPcap if precipitated,
as it includes a library required for live information capture
You also can download Wireshark’s supply code from this web page.
Wireshark,How to Capture Data Packets
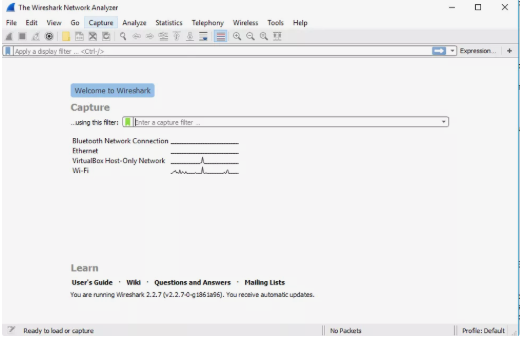
Wireshark,When you first release Wireshark, a welcome screen seems containing a list of available network connections on your present day tool. In this situation,
Displayed to the right of each is an EKG-style line graph that represents stay site visitors on that respective network.
To start taking pictures packets, select one or extra of the networks by way of clicking on your desire,
the usage of the Shift or Ctrl keys in case you need to file data from a couple of networks simultaneously.
Click on Capture within the main menu located toward the top of the Wireshark interface. When the drop-down menu seems, choose the Start alternative.
You also can initiate packet taking pictures via one of the following shortcuts.
- Keyboard: Press Ctrl + E.
- Mouse: To begin shooting packets from one particular community, double-click on on its call.
- Toolbar: Click on the blue shark fin button positioned on the a ways left aspect of the Wireshark toolbar.
- Keyboard: Press Ctrl + E
- Toolbar: Click at the pink Stop button placed next to the shark fin on the Wireshark toolbar.
Wireshark,Viewing and Analyzing Packet Contents
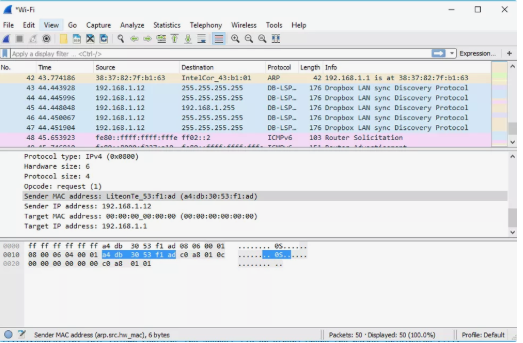
After you record a few community facts, it’s time to check the captured packets.
The captured records interface includes 3 important sections: the packet list pane, the packet details pane, and the packet bytes pane.
Wireshark,Packet List
The packet listing pane, placed at the top of the window, shows all packets discovered inside the active capture report.
Each packet has its very own row and corresponding wide variety assigned to it, together with each of those statistics points.
- Time:To alter this layout to some thing that could be a bit greater useful, including the actual time of day,
- pick out the Time Display Format option from Wireshark’s View menu placed at the pinnacle of the primary interface.
- Source: This column incorporates the deal with (IP or other) wherein the packet originated
- Protocol: The packet’s protocol name, along with TCP, may be located on this column.
- Info: Additional details about the packet are provided right here. The contents of this column can vary substantially relying on packet contents
- Open or closed brackets and a straight horizontal line indicate whether a packet.
- group of packets are all a part of the identical back-and-forth communique on the network.
A damaged horizontal line signifies that a packet isn’t a part of stated communique.
Packet Details
The info pane, discovered inside the middle, affords the protocols and protocol fields of the chosen packet in a collapsible format.
In addition to increasing every selection, you can practice character Wireshark filters based totally on specific details and,
comply with streams of information based totally on protocol kind thru the details context menu,
which is out there by using proper-clicking your mouse on the desired item on this pane.
Packet Bytes
At the lowest is the packet bytes pane, which presentations the uncooked information of the selected packet in a hexadecimal view.
This hex dump includes sixteen hexadecimal bytes and sixteen ASCII bytes alongside the records offset.
Selecting a specific portion of this information mechanically highlights its corresponding phase inside the packet info pane and vice versa. Any bytes that can’t be revealed are instead represented with the aid of a period.
You can pick to expose this statistics in bit format in place of hexadecimal by,
using right-clicking everywhere in the pane and selecting the perfect alternative from the context menu.
Using Wireshark Filters
One of the most critical function units in Wireshark is its filter functionality, especially whilst you’re coping with documents that,are sizeable in length.
educating Wireshark to best report the ones packets that meet your particular criteria.
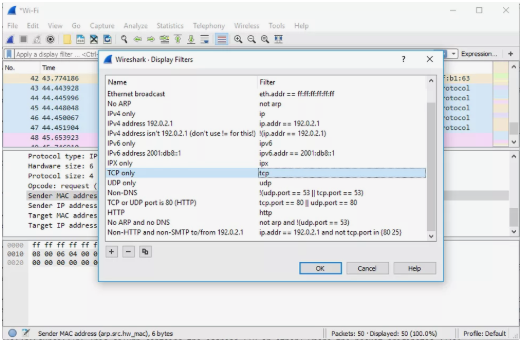
Wireshark presents a huge range of predefined filters by way of default,
letting you cut down the number of visible packets with only some keystrokes or mouse clicks.
To use such a existing filters, location its name in the Apply a display filter out entry subject placed directly below the Wireshark toolbar.
in the Enter a seize filter out entry subject placed in the middle of the welcome screen.
There are more than one methods to acquire this. If you recognize the name of your filter, kind it into the suitable discipline. For instance, if you most effective need to show TCP packets, you type tcp.
Wireshark’s autocompleting function indicates counseled names as you start typing, making it simpler to discover the perfect moniker for the filter out you’re looking for.
Another manner to pick a clear out is to click on on the bookmark-like icon located at the left facet of the entry subject.
This affords a menu containing a number of the maximum generally used filters as well as an choice to Manage Capture Filters or Manage Display Filters.
If you pick to manipulate either type, an interface appears permitting you to feature, get rid of, or edit filters.
You also can get admission to formerly used filters through choosing the down arrow at the proper side of the access discipline to show a history drop-down list.Once set, seize filters are carried out as quickly as you start recording community site visitors.
To observe a display filter out, you click on the right arrow button observed at the a long way right side of the access subject.
Color Rules
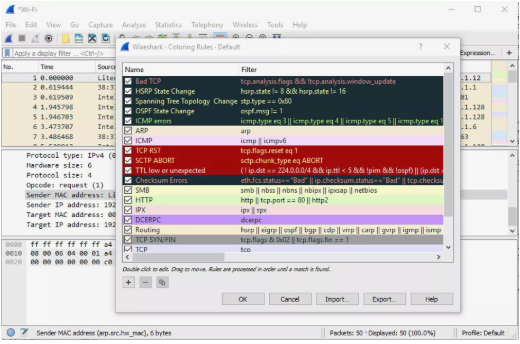
While Wireshark’s seize and display filters allow you to restrict which packets are recorded or proven on the display screen,
its colorization capability takes matters a step similarly via making it smooth to differentiate between distinctive packet kinds based totally on their person hue.
This reachable characteristic lets you fast find positive packets within a stored set by means of their row coloration within the packet listing pane.
Wireshark comes with about 20 default coloring rules constructed in, every of which may be edited, disabled, or deleted if you wish.
You can also add new shade-based totally filters via the coloring-regulations interface, accessible from the View menu.
In addition to defining a call and filter standards for each rule, you also are asked to partner each a background colour and a text coloration.
Packet colorization may be toggled on and off through the Colorize Packet List choice, also discovered in the View menu.
Statistics
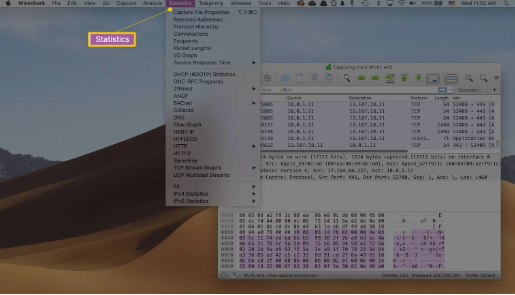
In addition to the specified statistics about your community’s statistics proven in Wireshark’s important window,
several other useful metrics are to be had thru the Statistics drop-down,
menu discovered in the direction of the pinnacle of the screen.
These encompass size and timing statistics approximately the seize document itself, along side dozens of charts and graphs ranging in subject matter from packet communique breakdowns to load distribution of HTTP requests.
Display filters may be carried out to a lot of those statistics through their interfaces,
and the results can be exported to numerous common record formats which include CSV, XML, and TXT.
Advanced Features
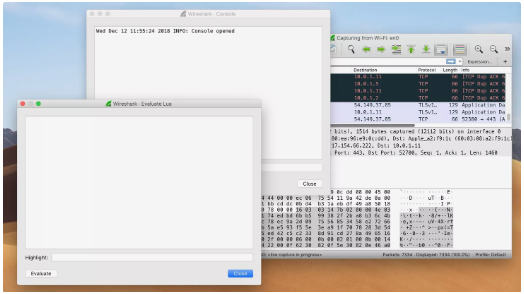
In addition to Wireshark’s main capability, there is additionally a group of additional capabilities to be had in this effective device normally reserved for superior customers.
This consists of the potential to write your own protocol dissectors inside the Lua programming language.