From http to https. AWS SSL install guide
INSTALL GUIDE. APACHE UBUNTU This element manual traces our adventure from http to https web page on AWS. There had been two motives for the flow. The first become the meant search engine marketing pickup that happens whilst you switch from http to https. The 2nd reason turned into the choice to provide a more at ease surroundings to our cellular and responsive subject users. We had received a few reports of consultation hijacking on inflamed clever telephones and we felt that it changed into time that we switched from http to https.
Our effort started out with a quick Google seek on installing SSL certificate on Amazon Web Services. The search results had been particularly useful however now not sufficient to assist me parent out what I had to do. Amazon Web Services documentation is hideously complex. All I need to know is if I even have a unmarried self managed instance with Apache on an Ubuntu server, how do I installation SSL? Considering the heartache /headache I had to undergo to get this performed I notion it might be assist to share this with others.
A few hints.
A) We made the move over 4 weekends length. Once you parent out the technique the circulate itself is painless however we desired to make sure that if a move associated outage took place it would have minimal traffic effect. We started out planning in mid March with the transfer in the end taking region in past due April.
B) In the first weeks we noticed a tremendous trade in site visitors signatures. Time on website, soar rates and web page perspectives consistent with session all shot up. But then slid again to significantly lower levels as compared to our pre-transition benchmarks. This can be because of an google replace that hit us end of April, early May but we aren’t positive. Our article posting frequency post the moe can also have had an effect on the drop in visitors.
C) The http to https transitions kills your original Quantcast implementation. Some tweaking is required to carry it lower back. You will even note a steep drop in your Google Webmaster dashboard but this is because you are still tracking the vintage http website. You want to add a new assets and resubmit your new sitemap with https links to tune your new site visitors consequences on webmaster. Google analytics works the same so there’s no trouble there.
D) Server and page velocity impact turned into large in each absolute and percentage phrases (kind of 30% slower) however no longer definitely noticeable at a person level. We went from 70 ms to ninety ms on server reaction and from 2 secs to 3 secs on page load speeds submit the move.
Below are the steps to install SSL certificates if:
- You are using a self managed instance on Amazon Web Services
- Operating System – Ubuntu 14.04
- Webserver – Apache
- Follows the Ubuntu/Debian layout of Apache files
- Your website uses WordPress
- Use a Mac with Terminal
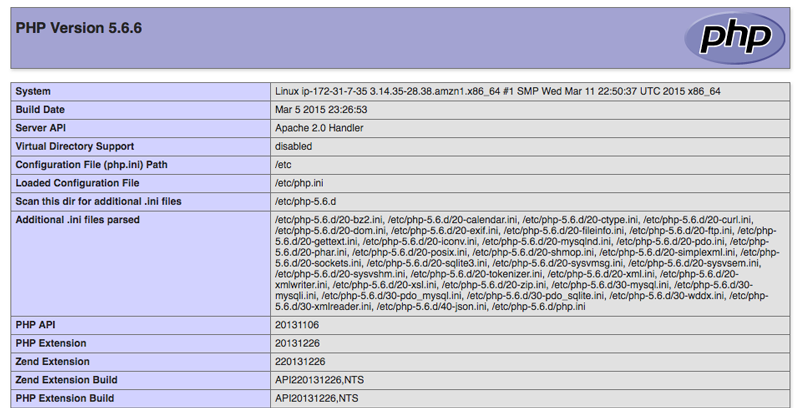
Step 1 –INSTALL GUIDE. APACHE UBUNTU Check if your AWS instance has OPENSSL installed
You will first have to check if OPENSSL is hooked up to your AWS server. By default, it is continually hooked up but to verify, type in the following command in your Terminal window:
sudo dpkg –s opensslThe results will show the following:
Package: openssl
Status: install ok installed
Version: 1.0.1f-1ubuntu2.19Step 2 — INSTALL GUIDE. APACHE UBUNTU Activate the SSL Module
SSL aid comes as widespread inside the Ubuntu 14.04 Apache package but; you may need to permit it. To allow the module run the command:
sudo a2enmod ssl
After you have enabled SSL, you will need to restart the server for the change to come into effect and handle SSL. Run the following command:
sudo service apache2 restart
Step 3 –INSTALL GUIDE. APACHE UBUNTU Generate a Certificate Signing Request (CSR) for your server and Private Key
A CSR or Certificate Signing request is a block of encrypted textual content that is generated on the server that the certificate can be used on. It includes information to be able to be included on your certificates.
First create a subdirectory wherein you may region the non-public key and the CSR file. Run the following command:
sudo mkdir /etc/apache2/ssl
Now from this directory, run the following command to generate a pair of private key and public Certificate Signing Request (CSR) for the webserver:
openssl req -nodes -newkey rsa:2048 -keyout myserver.key -out server.csr
Please note: for ease of use, it is recommended that you replace ‘server’ with the domain name the certificate will be issued for and similarly do that for the ‘myserver’ in the key file as well.
Now enter the details for your CSR:
Country Name (2 letter code) [AU]: GB State or Province Name (full name) [Some-State]: Surrey Locality Name (eg, city) []: London Organization Name (eg, company) [Internet Widgits Pty Ltd]: Company Name Pvt Ltd Organizational Unit Name (eg, section) []: IT Department Common Name (eg, YOUR name) []: yourdomain.com Email Address []:[email protected] A challenge password []: An optional company name []:
| ITEM | EXPLANATION |
| Country | Two-letter ISO code for the country where your organization is located |
| State or Province Name | State/region where your organization is located |
| Locality Name | City where your organization is located |
| Organization Name | Full legal name of your organization |
| Organizational Unit Name | Division of your organization handling the certificate |
| Common Name (server FQDN) | Fully qualified domain name (FQDN) of your server |
| Email address | An email address used to contact your organization |
The key and certificates might be created and placed in your /and so forth/apache2/ssl listing.The fields email cope with, optional organization name and assignment password can be left blank. If you enter ‘.’, the sphere could be left clean.
The above command will create 2 documents.
The myserver.Key document is the Private Key, with the intention to be used for decryption of the SSL/TLS session among a server and a purchaser. It seems like the subsequent if you open the report in a textual content editor:
—–BEGIN PRIVATE KEY—– 3v9zk……………………… dLxa/s= —–END PRIVATE KEY—–
Do not proportion this document and make sure which you have a backup of the personal key as it’s far can be not possible to install the certificate with out it at the server afterwards.
The server.Csr document incorporates the CSR code that you will need to publish during the certificate activation system. The CSR will appear to be the subsequent if you open the report in a textual content editor:
—–BEGIN CERTIFICATE REQUEST—– MIIByjCCATMCAQAwgYkxCzAJBgNVBAYTAlVTMRMwEQYDVQQIEwpDYWxpZm9ybmlh …. —–END CERTIFICATE REQUEST—–
Step 4 – INSTALL GUIDE. APACHE UBUNTU Buy or get a trial SSL Certificate
You can both purchase a SSL certificate or attempt out ones which are available for a 90-day trial period. For my own testing functions I used Comodo’s Free SSL Certificate.
Once you have generated the CSR, you will want to provide it to the certificate authority to difficulty the SSL certificate. Before the certificate authority problems the SSL certificates, it will want to validate domain manipulate i.E. That you manage the domain for which the certificate is being requested. The domain manipulate validation can manifest in one in every of 3 approaches:
1. INSTALL GUIDE. APACHE UBUNTU Email based validation
Select the e-mail recipient i.E. The registrar of the area or the administrator contact of the domain i.E.. Webmaster/[email protected]. An e mail will be sent to the executive touch containing a completely unique validation code and hyperlink. Click the link and enter the code to verify domain control.
2. INSTALL GUIDE. APACHE UBUNTU DNS CNAME based validation
If you select this option, then Comodo will provide you with the hash values which must be entered as a DNS CNAME record for your domain.
The hashes are to be entered as follows:
.yourdomain.com. CNAME .comodoca.com.
3. HTTP based validation
If you pick out this feature, then Comodo will offer you with the hash values which ought to used to create a plain-text record which wishes to be positioned in the root of yourdomain’s listing and served over HTTP-handiest.
The file and it’s content should be as follows: http://yourdomain.com/<Upper case value of MD5 hash of CSR>.txt
Content (as a plain text file): <Value of SHA1 hash of CSR> comodoca.com
On affirmation of area manipulate, the certificate authority will difficulty your SSL certificate. The SSL certificates can be furnished as a zip file so that it will incorporate the following 2 files:
- ca-bundle
- crt
You need to replicate those files to the listing to your server where you will keep your certificates and key files via the use of a FTP program, in our case /and so forth/apache2/ssl.
Step 5 – Install the SSL Certificate on your webserver
Copy your SSL certificate file (www_yourdomain_com.crt) and the certificate bundle file (www_yourdomain_com.ca-bundle) to your Apache server. Your private key file should already be on the server from when you generated your certificate request (CSR) at the location /etc/apache2/ssl.
Create 2 additional directories in /etc/apache2/ssl:
sudo mkdir /etc/apache2/ssl/keysudo mkdir /etc/apache2/ssl/certs- key – this is where you will store the Private key
- certs – this is where you will store the .ca-bundle and .crt files received from the certificate authority
Step 6 — INSTALL GUIDE. APACHE UBUNTUConfigure Apache to use SSL
Now that you have the certificate and key available on the webserver, lets configure Apache to use these files in a virtual host file.
Go to the following location – /etc/apache2/sites-available/ and open the file default-ssl.conf by typing the command:
sudo nano /etc/apache2/sites-available/default-ssl.conf
Without the comments, the file looks like this:
<IfModule mod_ssl.c>
<VirtualHost _default_:443>
ServerAdmin webmaster@localhost
DocumentRoot /var/www/html
ErrorLog ${APACHE_LOG_DIR}/error.log
CustomLog ${APACHE_LOG_DIR}/access.log combined
SSLEngine on
SSLCertificateFile /etc/ssl/certs/ssl-cert-snakeoil.pem
SSLCertificateKeyFile /etc/ssl/private/ssl-cert-snakeoil.key
<FilesMatch “\.(cgi|shtml|phtml|php)$”>
SSLOptions +StdEnvVars </FilesMatch>
<Directory /usr/lib/cgi-bin>
SSLOptions +StdEnvVars
</Directory>
BrowserMatch “MSIE [2-6]”
\ nokeepalive ssl-unclean-shutdown
\ downgrade-1.0 force-response-1.0
BrowserMatch “MSIE [17-9]” ssl-unclean-shutdown
</VirtualHost>
</IfModule>We will configure for a virtual host (ServerAdmin, ServerName, ServerAlias, DocumentRoot, and many others.) as well as change the region of in which Apache looks for the SSL certificates and key.
Add the following item in the file right after “ServerAdmin”:
- ServerName yourdomain.com
Change only the following items in the file:
- ServerAdmin webmaster@localhost
- ServerAlias yourdomain.com
- DocumentRoot /var/www/yourdomain/
- SSLEngine on
- SSLCertificateFile /etc/ssl/ssl.certs/www_yourdomain_com.crt
- SSLCertificateKeyFile /etc/ssl/ssl.key/myserver.key
- SSLCertificateChainFile /etc/ssl/ssl.cert/www_yourdomain_com.ca-bundle
Press Control + X and then select ‘Y’ to save your changes.
Step 7 — INSTALL GUIDE. APACHE UBUNTU Activate the SSL Virtual Host
Now that we have configured the SSL-enabled virtual host, we need to enable it.
Run the following command:
sudo a2ensite default-ssl.conf
You will need to restart the server for the changes to come into effect. Run the following command:
sudo service apache2 restart
This should enable your new virtual host, which will serve encrypted content using the SSL certificate you created.
Step 8 — INSTALL GUIDE. APACHE UBUNTU Test that you have setup SSL correctly
Test that your SSL certificate has been correctly installed by going to the following site and entering your URL.
The plugin mechanically detects your settings and configures your website. Just install the plugin and viola you’re carried out! The website online url and domestic url may be modified to https and all of your content http:// urls will be replaced with the https:// urls.
Congratulations … you have now effectively mounted SSL on AWS
Useful links
- https://www.digitalocean.com/community/tutorials/how-to-create-a-ssl-certificate-on-apache-for-ubuntu-14-04
- https://www.digicert.com/ssl-certificate-installation-apache.htm
- https://www.namecheap.com/support/knowledgebase/article.aspx/794/67/how-do-i-activate-an-ssl-certificate
- https://www.sslshopper.com/ssl-checker.html
- https://wordpress.org/plugins/really-simple-ssl/
Related Posts
*Estimating WordPress traffic on AWS servers. *The AWS guide that will make you switch to Reserved EC2 Instances